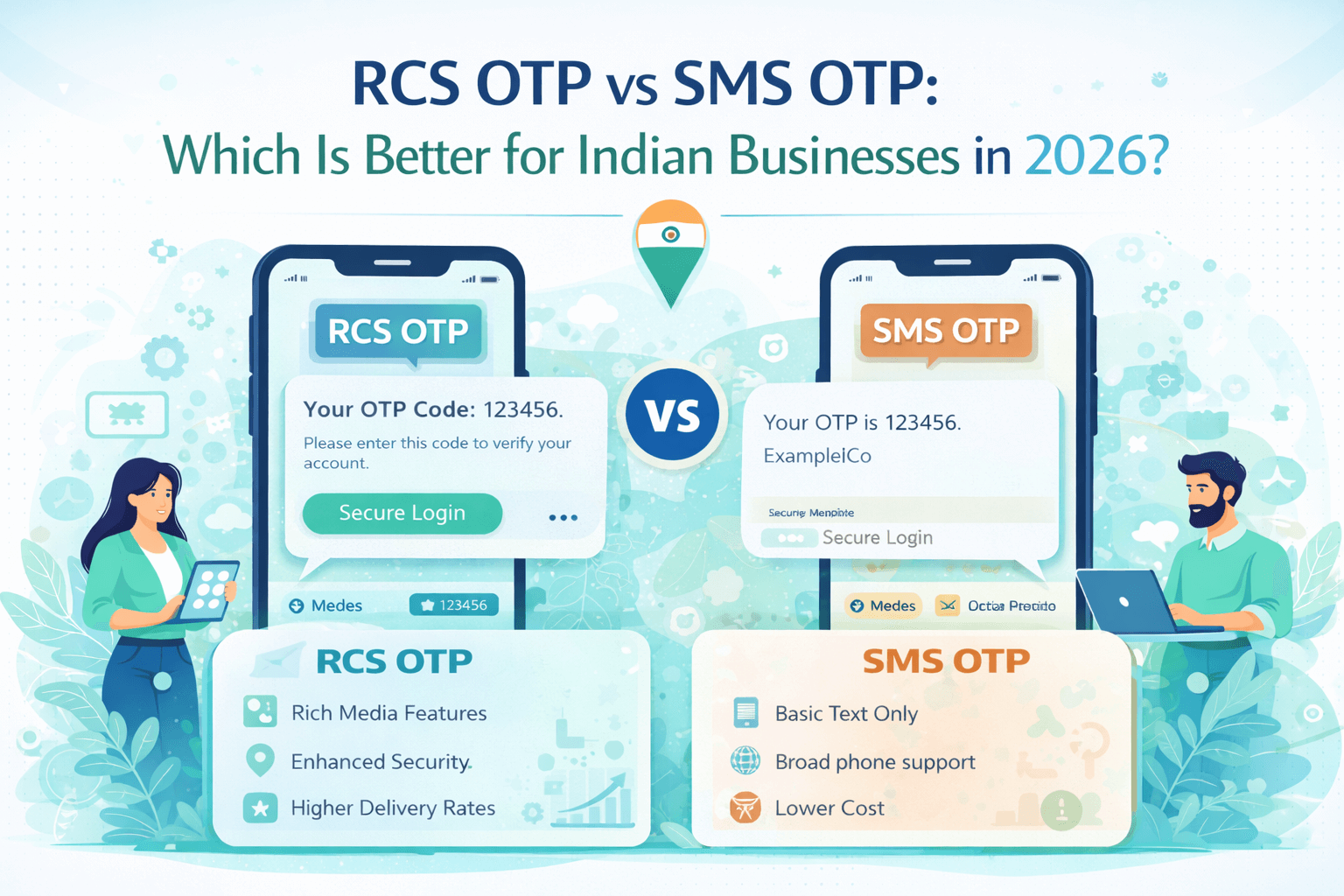
RCS OTP vs SMS OTP: Which Is Better for Indian Businesses in 2026?
RCS OTP vs SMS OTP for India — security, cost, delivery speed, fraud resistance compared. Find out which is better for your Indian business in 2026
RCS OTP vs SMS OTP: Which Is Better for Indian Businesses in 2026?
Every
time an Indian user logs into their bank account, completes a UPI payment,
registers on an app, or resets a password — they receive an OTP (One-Time
Password). OTPs are the backbone of digital security in India, with billions of
OTP messages sent every month across fintech, banking, e-commerce, healthcare,
and government services.
Traditionally,
these OTPs have been delivered via SMS — a reliable but increasingly vulnerable
channel. In 2026, a new challenger has emerged: RCS OTP. Rich Communication
Services brings significant improvements in security, user experience, and
fraud resistance over traditional SMS OTP.
But is RCS OTP actually better for Indian businesses? Or is SMS OTP still the safer, more reliable choice given India's diverse device landscape? This in-depth guide answers that question — with a detailed comparison across 15+ criteria, India-specific data, real-world examples, and clear recommendations for different business types.
OTP
(One-Time Password) is a temporary, automatically generated code used to verify
a user's identity for a single transaction or login session. OTPs are valid for
a short window — typically 30 seconds to 10 minutes — and become invalid once
used.
In
India, OTP-based authentication is mandated or strongly recommended by key
regulatory bodies:
● RBI
(Reserve Bank of India): Mandates 2FA with OTP for all online banking
transactions above ₹5,000
● SEBI:
Requires OTP authentication for investment account access and transactions
● IRDAI:
Insurance policy access and claims require OTP verification
● TRAI:
Regulates OTP delivery through DLT framework — all OTP senders must be
registered
● CERT-In: Recommends OTP as part of multi-factor authentication for critical digital infrastructure
Scale of OTP Usage in India
India
processes an estimated 5-8 billion OTP messages every month — making it one of
the world's largest OTP markets. Key drivers include:
● UPI
Transactions: Over 10 billion UPI
transactions per month in 2026, most requiring OTP or PIN verification
● Digital
Banking: 500+ million active digital
banking users generating multiple OTPs daily
● E-commerce:
Flipkart, Amazon India, Meesho, and
Myntra combined send hundreds of millions of OTPs monthly
● Fintech
Apps: Paytm, PhonePe, CRED, Groww,
Zerodha — all heavy OTP users
● Government Services: Aadhaar-based OTP authentication for DigiLocker, UMANG, income tax portal
SMS OTP is the traditional method of sending one-time passwords via plain text messages to a user's mobile number. Despite being the dominant OTP channel in India today, SMS OTP has well-documented weaknesses that cost Indian businesses and consumers crores of rupees annually.
How SMS OTP Works
1. User
initiates an action (login, payment, registration) on an app or website
2. The
business's backend generates a random OTP (typically 4-6 digits)
3. The
OTP is sent to the user's registered mobile number via an SMS gateway
4. The
message travels through TRAI's DLT platform for compliance verification
5. The
carrier (Jio/Airtel/Vi/BSNL) delivers the SMS to the user's SIM
6. User
reads the OTP from the notification and types it into the app
7. The app verifies the OTP and grants access
Critical Limitations of SMS OTP in India
● SIM Swap
Fraud: India reports 15,000-20,000 SIM
swap fraud cases annually. Fraudsters convince carriers to transfer a victim's
number to a new SIM, intercepting all OTPs. This has cost Indian bank customers
hundreds of crores.
● SS7
Network Vulnerability: SMS travels over
the SS7 (Signaling System 7) network, which has known security vulnerabilities
that allow sophisticated attackers to intercept messages without physical
access to the SIM.
● OTP
Auto-Read Malware: Android malware that
reads SMS OTPs automatically is a major threat in India — particularly
prevalent on budget Android devices popular in tier-2/3 markets. Apps like
'battery savers' or fake utility apps often carry SMS-reading malware.
● Phishing
via Fake SMS: Fraudsters send fake SMS
messages mimicking bank OTPs, tricking users into entering codes on phishing
websites. The Indian Cyber Crime Coordination Centre (I4C) reports this as one
of the top digital fraud vectors.
● No
Delivery Confirmation: SMS provides no
read receipts — businesses cannot confirm whether the OTP was actually seen by
the legitimate user versus intercepted by a fraudster.
● Notification
Banner Visibility: SMS OTPs appear in
the notification banner, visible to anyone near the device — a privacy risk in
public spaces.
● DLT Delays: India's mandatory DLT scrubbing of SMS adds 1-3 seconds of latency to every OTP delivery — critical for time-sensitive payment flows.
RCS OTP is the delivery of one-time passwords through the RCS (Rich Communication Services) protocol instead of SMS. In the RCS model, the OTP is delivered as a verified, rich message from a confirmed business identity — with cryptographic protections that SMS fundamentally lacks.
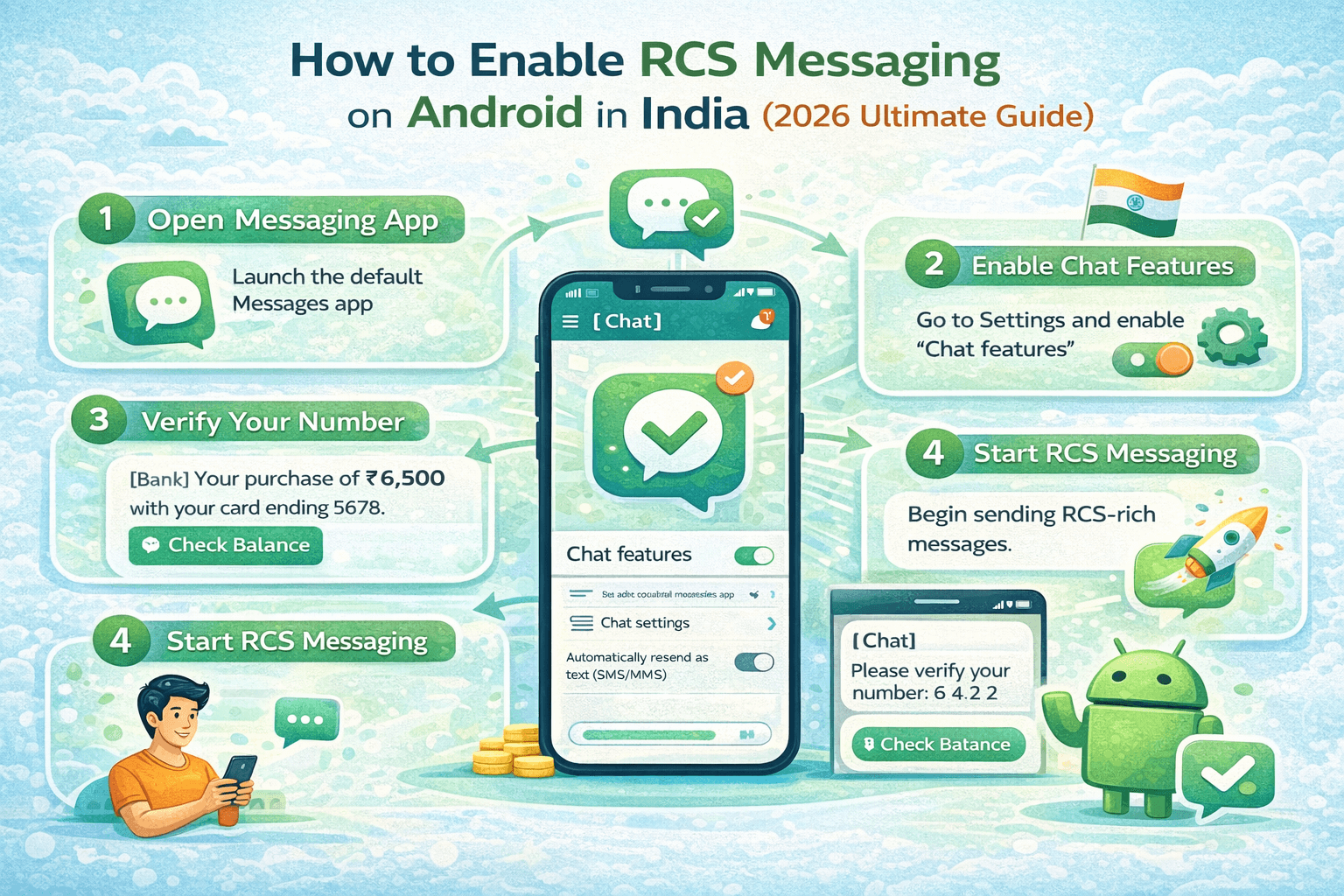
How RCS OTP Works
1. User
initiates authentication on an app or website
2. The
backend generates the OTP and sends it via the RCS Business Messaging API
3. The
message is delivered over the internet (IP-based) — not the vulnerable SS7
telephony network
4. The
RCS message arrives in the user's native messaging app (Google Messages on
Android) with a verified business sender badge
5. The
user sees the OTP in a visually distinct, branded message — with the company
logo, verified checkmark, and optional auto-fill capability
6. On
modern Android devices (Android 11+), the OTP can auto-populate in the app
field — zero manual entry required
7. The OTP is verified and the session proceeds
Security Architecture of RCS OTP
RCS
OTP's security advantage over SMS stems from fundamentally different technical
architecture:
● IP-based
delivery: RCS messages travel over
encrypted IP networks (similar to HTTPS web traffic) — not the legacy SS7
telephony network. This eliminates the SS7 interception attack vector entirely.
● End-to-end
message integrity: RCS Business Messages
are cryptographically signed by the sender and verified by Google's RCS
infrastructure — ensuring the message cannot be tampered with in transit.
● Verified
sender identity: Every RCS OTP arrives
from a Google-verified business identity with a blue checkmark and brand logo.
Users can instantly confirm the message is from the legitimate business — not a
spoofed sender.
● No
SIM-based vulnerability: Since RCS
delivery is IP-based and tied to the device's Google account (not just the
SIM), SIM swap attacks do not intercept RCS OTPs — the message still goes to
the original account holder's device.
● Android auto-fill integration: RCS OTPs can be auto-detected by Android's Smart Lock and filled automatically — reducing the window where a user might be tricked into entering an OTP on a phishing site.
Here is a comprehensive comparison across every dimension that matters to Indian businesses choosing an OTP delivery channel:
Security Comparison
|
Security
Factor |
SMS OTP |
RCS OTP |
|
SIM Swap
Vulnerability |
🔴
HIGH RISK — SIM swap intercepts SMS |
🟢
PROTECTED — IP-based, not SIM-bound |
|
SS7 Network
Attacks |
🔴
VULNERABLE — travels over SS7 |
🟢
SAFE — IP network, no SS7 |
|
Malware OTP
Theft |
🔴 AT
RISK — SMS readable by apps |
🟡
LOWER RISK — harder to intercept |
|
Sender
Verification |
🔴
NONE — any number can spoof |
🟢
VERIFIED — Google-confirmed sender |
|
Phishing
Resistance |
🔴 LOW
— fake SMS looks identical |
🟢
HIGH — verified badge visible |
|
Message
Tampering |
🔴
POSSIBLE — plain text in transit |
🟢
PROTECTED — cryptographically signed |
|
Overall
Security Score |
🔴
POOR — multiple critical vulnerabilities |
🟢
STRONG — multi-layer protection |
Performance & Delivery Comparison
|
Performance
Factor |
SMS OTP |
RCS OTP |
|
Average
Delivery Time (India) |
3-8 seconds (incl. DLT delay) |
1-3 seconds (IP-based) |
|
Delivery Rate
(Jio/Airtel) |
96-98% (mature infrastructure) |
88-94% (growing adoption) |
|
Delivery Rate
(Vi/BSNL) |
92-96% |
80-90% |
|
Works Without
Internet |
✅ Yes — cellular only |
❌ No — needs data connection |
|
Works on
Feature Phones |
✅ Yes — universal |
❌ No — Android required |
|
Fallback
Available |
N/A — is the fallback |
✅ Auto falls back to SMS |
|
Read Receipt |
❌ No confirmation |
✅ Delivery + read confirmed |
User Experience Comparison
|
UX Factor |
SMS OTP |
RCS OTP |
|
Message
Appearance |
Plain text, no branding |
Branded — logo, colors, verified badge |
|
Auto-Fill
Support |
Basic (Android 9+) |
Advanced (Android 11+ native) |
|
User Trust
Signal |
Anonymous number |
Verified company identity |
|
Notification
Style |
Standard SMS notification |
Rich notification with branding |
|
Message
Length |
Limited — fits in SMS |
Unlimited — can include instructions |
|
Accessibility |
Works on all devices |
Android smartphones only (for now) |
|
UX Score
(India) |
3/5 — familiar but plain |
4.5/5 — modern, trusted, smooth |
Cost Comparison (India 2026)
|
Cost Factor |
SMS OTP |
RCS OTP |
|
Per Message
Cost (India) |
₹0.15–₹0.25/message |
₹0.20–₹0.40/message |
|
DLT
Registration Cost |
₹1,000–₹5,000 (one-time) |
Included in most RCS plans |
|
Fraud Loss
Cost (avg) |
₹8–₹25 per fraud incident |
₹1–₹5 (much lower fraud rate) |
|
Total Cost of
Ownership |
Higher when fraud included |
Lower when fraud savings counted |
|
Volume
Discount (1Cr msgs) |
₹0.10–₹0.15/message |
₹0.15–₹0.25/message |
|
Free Fallback
Cost |
N/A |
SMS cost if RCS fails (~10-12%) |
Here is the overall comparison scorecard across 8 key dimensions for Indian businesses:
|
Dimension |
SMS OTP |
RCS OTP |
Winner &
Why |
|
Security |
4/10 |
9/10 |
RCS —
IP-based, verified, fraud-resistant |
|
Delivery
Speed |
7/10 |
9/10 |
RCS — faster
IP delivery, no DLT delay |
|
Device
Coverage (India) |
10/10 |
7/10 |
SMS — works
on all phones including basic |
|
User
Experience |
6/10 |
9/10 |
RCS —
branded, auto-fill, verified sender |
|
Fraud
Resistance |
3/10 |
9/10 |
RCS —
eliminates SIM swap, SS7 attacks |
|
Cost
Efficiency |
8/10 |
7/10 |
SMS — lower
per-message cost (without fraud) |
|
Compliance
(TRAI/RBI) |
8/10 |
8/10 |
TIE — both
compliant with proper setup |
|
Future
Readiness |
5/10 |
9/10 |
RCS — growing
adoption, modern standard |
Overall Score Summary
|
52/80 SMS OTP |
Reliable and
universal, but vulnerable to fraud, lacks verification, and delivers a poor
user experience on modern devices. |
|
68/80 RCS OTP |
Superior
security, better UX, and stronger fraud resistance — with the only
significant weakness being incomplete device coverage in India
(non-Android/non-RCS devices). |
Industry-Specific Recommendations for India
The right OTP strategy varies by industry, customer base, and regulatory requirements. Here are specific recommendations for key Indian sectors:
1. Banking and NBFCs
For
RBI-regulated banks and NBFCs, OTP security is a critical compliance
requirement. RCS OTP is strongly recommended because:
● SIM
swap fraud is the #1 digital banking fraud vector in India — RCS eliminates
this risk
● Verified
sender badge reduces OTP phishing susceptibility significantly
● RBI's
digital payment security guidelines align with RCS's stronger authentication
model
● Recommended
implementation: RCS OTP as primary, SMS OTP as fallback
● Best RCS OTP providers for banks: Kaleyra, Tanla/Karix, Gupshup
2. Fintech and Payment Apps
Payment
apps (UPI, wallets, lending) handle high-frequency, high-value transactions
where OTP security is critical and user experience directly impacts conversion
rates:
● RCS
auto-fill capability reduces OTP entry friction — improving payment completion
rates by 15-25%
● Branded
OTP messages increase user trust in a market where payment fraud is common
● For
UPI-based apps, faster RCS delivery (vs SMS DLT delay) means smoother payment
flows
● Recommended
implementation: RCS OTP primary with SMS fallback for non-RCS devices
● Best for: Paytm-style apps, digital lending platforms, investment apps
3. E-Commerce and Quick Commerce
Indian
e-commerce platforms send OTPs for login, order confirmation, and return/refund
verification. For platforms targeting urban, smartphone-native customers:
● RCS
branded OTPs increase customer trust — especially for new users unfamiliar with
the brand
● Auto-fill
reduces drop-offs during checkout — a direct revenue impact
● For
quick commerce (10-minute delivery apps), RCS's faster delivery is
operationally important
● For
tier-2/3 markets with older devices, maintain robust SMS fallback
● Recommended split: RCS for Android users in metro/tier-1 cities, SMS for all others
4. Healthcare and Telemedicine
Healthcare
OTPs are used for patient login, prescription access, and health record
verification. Privacy and security are paramount:
● RCS
OTP's verified sender prevents medical identity theft
● Branded
hospital/clinic identity in OTP messages builds patient trust
● Auto-fill
is particularly valuable for elderly patients who struggle with manual OTP
entry
● Consider
patient demographics — older patients may be on older devices without RCS
support
● Recommended: RCS OTP with SMS fallback; prioritize SMS for elderly patient populations
5. Government and Public Services
DigiLocker,
UMANG, income tax portal, and other Aadhaar-linked services serve India's
entire population — including users on basic smartphones and feature phones:
● SMS
OTP remains essential for government services due to universal device coverage
requirements
● RCS
OTP can be offered as a premium option for urban Android users
● Aadhaar
OTP (sent via UIDAI) is SMS-based and unlikely to shift to RCS in the near term
● Recommended: SMS primary for broad coverage, RCS as optional enhanced security for urban users
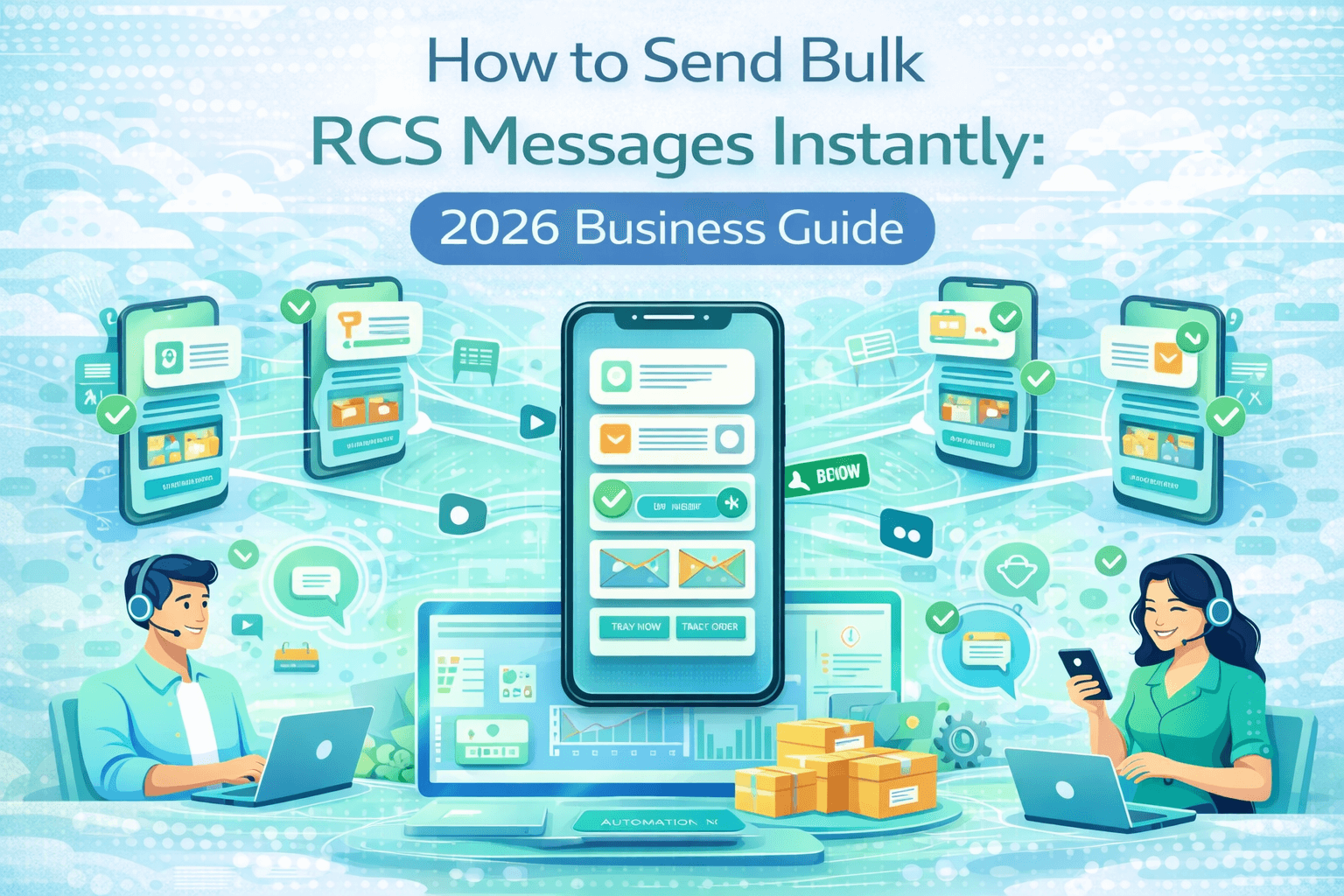
Switching from SMS OTP to RCS OTP (with fallback) in India involves these key steps:
Step 1: Choose an RCS OTP Provider with India Coverage
Select a provider that offers both RCS OTP and SMS fallback from a single API endpoint. Recommended options for India: Gupshup, Route Mobile, Kaleyra, or Tanla/Karix. Verify they support all major Indian carriers — Jio, Airtel, Vi, and BSNL.
Step 2: Complete DLT Registration
Register your OTP sender ID on India's DLT platform. OTP messages fall under the 'Transactional' category in TRAI's DLT framework. Registration requires: GST certificate, business PAN, registered sender ID, and approved OTP message template.
Step 3: Design Your RCS OTP Template
Create an RCS OTP template that includes: your company logo, verified sender name, the OTP prominently displayed, expiry time clearly stated, and a security notice ('Do not share this OTP with anyone'). Submit for Google RCS Business Messaging approval (1-3 days).
Step 4: Integrate the API
Most providers offer a single API endpoint that handles the RCS/SMS routing logic automatically. Your backend sends one API call — the provider attempts RCS first, and falls back to SMS if the device doesn't support RCS. Key parameters to set: OTP length (6 digits recommended), expiry time (5 minutes recommended), retry logic.
Step 5: Test Across Device Types
Test your RCS OTP on: Google Messages (Android 11+), Samsung Messages (Galaxy), older Android devices (fallback to SMS), and iPhones (SMS fallback). Verify auto-fill works on supported devices and that the branded appearance renders correctly.
Step 6: Monitor and Optimize
Track key metrics: RCS delivery rate vs SMS fallback rate, OTP completion rate, fraud attempt rate, and average delivery time. Most Indian RCS providers offer real-time analytics dashboards showing these metrics by device type and carrier.
Frequently Asked Questions (FAQs)
India-specific questions businesses ask about RCS OTP vs SMS OTP:
|
Q1: Is RCS OTP approved by
RBI for banking transactions in India? |
|
RBI's
guidelines mandate two-factor authentication for online banking but do not
specify SMS as the only permitted OTP channel. RCS OTP, when properly
implemented with verified sender identity and secure delivery, meets RBI's
OTP security requirements. However, businesses should consult with their
compliance team and RBI guidelines specific to their banking license category
before switching. |
|
Q2: Does RCS OTP work on
Jio and Airtel networks in India? |
|
Yes. Both Jio
and Airtel support RCS on their 4G and 5G networks in India. Google Messages
(pre-installed on most Jio and Airtel Android devices) handles RCS delivery
natively. RCS OTP delivery works on all Android devices running Google
Messages or Samsung Messages on Jio and Airtel. Vi support is also available
but slightly less consistent. |
|
Q3: What happens to the OTP
if the user's phone doesn't support RCS? |
|
If a user's
device doesn't support RCS, the OTP automatically falls back to SMS delivery.
This fallback happens seamlessly — the user receives an SMS OTP without any
error or delay. Most Indian RCS OTP providers handle this fallback
automatically within their API, so your backend sends a single API call
regardless of the delivery method used. |
|
Q4: Is RCS OTP protected
against SIM swap fraud in India? |
|
Yes — this is
RCS OTP's most significant security advantage for India. SIM swap fraud works
by transferring a victim's phone number to a new SIM, allowing the fraudster
to receive SMS OTPs. RCS OTP is tied to the user's Google account and device
— not just the SIM card. Even if a fraudster successfully swaps the SIM, they
cannot receive RCS OTPs without access to the original device and Google
account. |
|
Q5: How much does RCS OTP
cost compared to SMS OTP in India? |
|
RCS OTP
typically costs ₹0.20–₹0.40 per message versus ₹0.15–₹0.25 for SMS OTP —
approximately ₹0.05–₹0.15 more per message. However, when you factor in fraud
savings (RCS reduces OTP fraud by 60-80%) and the cost of SMS fallback (only
10-12% of messages), the total cost of ownership is often lower with RCS OTP
for businesses experiencing significant OTP fraud. |
|
Q6: Does RCS OTP require
DLT registration in India? |
|
Yes. Even
though RCS OTP travels over IP networks, businesses sending OTPs to Indian
mobile numbers are still required to comply with TRAI's DLT framework. Your
sender ID and OTP template must be registered on an approved DLT platform.
Most Indian RCS OTP providers include DLT registration assistance in their
onboarding process. |
|
Q7: Can iPhone users in
India receive RCS OTP? |
|
iPhone users
running iOS 18 or later can receive RCS messages, including RCS OTP. However,
iPhone's RCS implementation may not support all advanced RCS OTP features
like auto-fill. For iPhone users on iOS 17 or earlier, messages fall back to
SMS automatically. Given iPhone's 4-5% market share in India, SMS fallback
handles the vast majority of non-RCS scenarios. |
|
Q8: Is the auto-fill
feature for RCS OTP available in India? |
|
Yes.
Android's Smart Lock OTP auto-fill works with RCS OTP on Android 11+ devices
(which cover the majority of Android smartphones sold in India in 2022 and
later). The auto-fill detects the OTP code in the RCS message and
automatically populates it in the app field — eliminating manual entry and
reducing the phishing risk of users entering OTPs on fake websites. |
|
Q9: Which Indian banks are
currently using RCS OTP? |
|
Several
leading Indian private banks and fintech companies have piloted or deployed
RCS OTP in 2025-2026, including HDFC Bank, Axis Bank, and several major
fintech platforms. Public sector banks are moving more cautiously due to
their broader customer base including feature phone users. As RCS coverage
improves, adoption across Indian banking is expected to accelerate
significantly. |
|
Q10: Should I completely
replace SMS OTP with RCS OTP in India? |
|
No — a
complete replacement is not recommended in 2026 given India's device
diversity. The recommended strategy is RCS-first with automatic SMS fallback:
attempt RCS OTP delivery first, automatically fall back to SMS if the device
doesn't support RCS. This gives you RCS security benefits for the 65-70% of
users who support it, while maintaining 100% coverage for the remaining
users. |
Conclusion: RCS OTP Is the Future, SMS OTP
Is Still the Safety Net
The
verdict is clear: RCS OTP is the superior authentication channel for Indian
businesses in 2026 across every security and user experience dimension. Its
IP-based delivery, verified sender identity, and SIM-swap resistance directly
address the fraud vulnerabilities that cost Indian businesses and consumers
thousands of crores annually.
However, SMS OTP remains essential as a fallback channel — India's diverse device landscape means you cannot abandon SMS entirely without losing coverage for a significant portion of your users. The winning strategy is not SMS or RCS — it's SMS and RCS together, intelligently routed.
● Security
priority businesses (banks, fintech, insurance): Switch to RCS OTP immediately — fraud savings justify the
slightly higher per-message cost.
● E-commerce
and consumer apps: Implement RCS OTP for
metro and tier-1 users, maintain SMS for tier-2/3 and older devices.
● Government
and public services: Maintain SMS
primary for broad coverage, pilot RCS for urban Android segments.
● Healthcare: RCS OTP recommended for working-age patients on modern devices; SMS essential for elderly populations.
The
businesses that switch to RCS OTP today gain a security and trust advantage
that will compound as RCS adoption continues to grow across India. With Jio and
Airtel actively promoting RCS to their Android user bases, RCS coverage in
India is expected to exceed 80% of smartphone users by 2027.